Worldwide Sweep Targets Business Email Compromise [Operation reWired]
The FBI and federal partners have announced scores of arrests in the United States and overseas in a coordinated law enforcement sweep targeting perpetrators of an insidious scam that tricks businesses and individuals into wiring money to criminals.
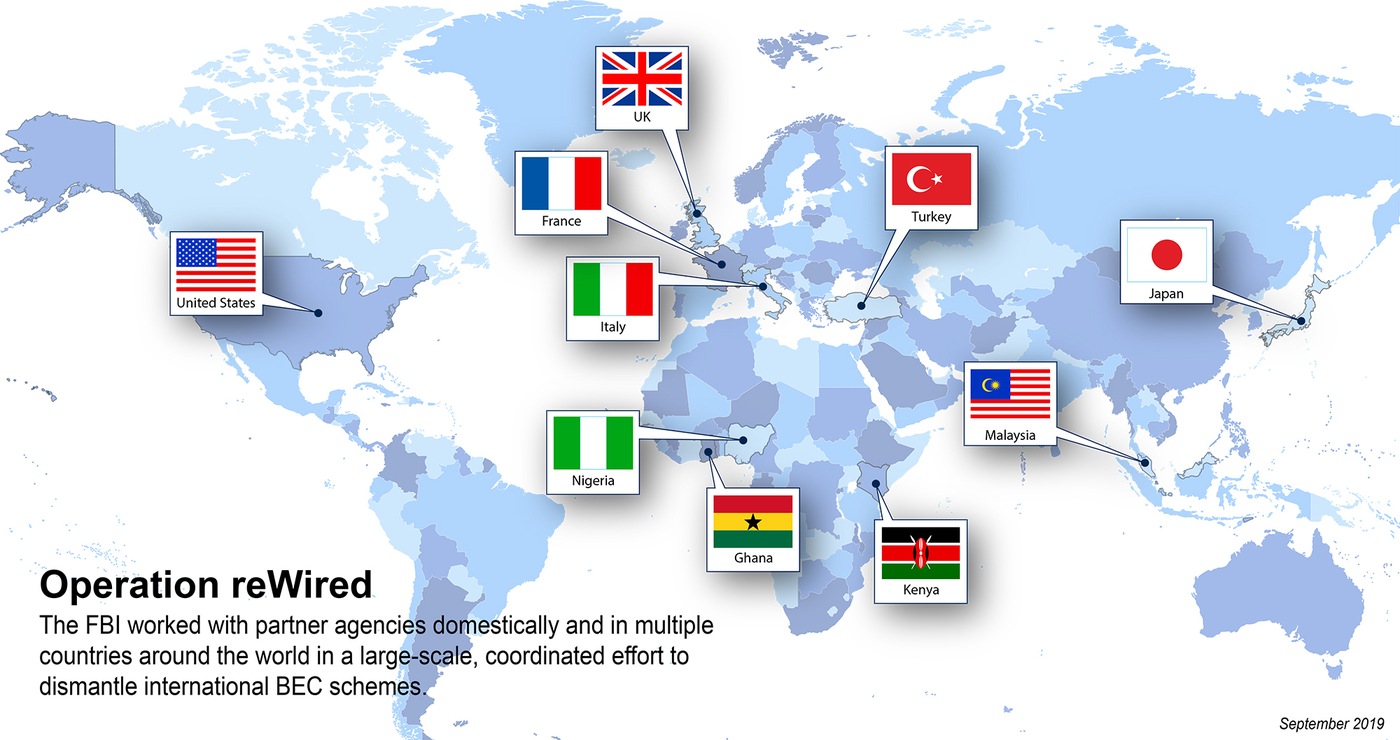
Operation reWired, a months-long, multi-agency effort to disrupt and dismantle international business email compromise (BEC) schemes, resulted in 281 arrests, including 74 in the United States, officials announced. Arrests were also made in Nigeria, Turkey, Ghana, France, Italy, Japan, Kenya, Malaysia, and the United Kingdom. The sweep resulted in the seizure of nearly $3.7 million and the disruption and recovery of approximately $118 million in fraudulent wire transfers.
These sophisticated cyber-enabled scams often target employees with access to company finances and—using methods like social engineering and computer intrusions—trick them into making wire transfers to bank accounts thought to belong to trusted partners. The accounts are actually controlled by the criminals.
The operation follows last year’s Operation WireWire, a similar effort that led to total 74 arrests and the seizure of $2.4 million. Thirty-nine of the FBI’s 56 field offices participated in this year’s sweep alongside state and local task force officers and partner agencies, including the Department of Homeland Security, Department of State, Department of the Treasury, and the U.S. Postal Inspection Service.
The effects of this crime are far-reaching, and the dollar amounts involved are staggering. Since the Internet Crime Complaint Center (IC3) began formally tracking BEC (and its variant, email account compromise, or EAC) in 2013, it has gathered reports of more than $10 billion in losses from U.S. victims alone. The worldwide tally is more than $26 billion.
“The FBI is working every day to disrupt and dismantle the criminal enterprises that target our businesses and our citizens,” said FBI Director Christopher Wray. “Through Operation reWired, we’re sending a clear message to the criminals who orchestrate these BEC schemes: We’ll keep coming after you, no matter where you are.”
Criminal organizations that perpetrate BEC schemes don’t just target companies. They also exploit individual victims—such as real estate purchasers or the elderly—by convincing them to make wire transfers to bank accounts controlled by the criminals. The scam can also involve requests to purchase gift cards and send the serial numbers or to mail a check, but the request will always appear to come from someone known to or trusted by the victim.
“Through Operation reWired, we’re sending a clear message to the criminals who orchestrate these BEC schemes: We’ll keep coming after you, no matter where you are.”
FBI Director Christopher Wray
An FBI case that was part of last year’s operation illustrates how the BEC scheme works: Beginning in 2015, two men working remotely from the United Kingdom and Nigeria sent emails to an executive at a Connecticut-based company appearing to be from the company’s CEO, who was also located overseas. The purported CEO was requesting a wire transfer of funds. The email looked legitimate, so the company’s controller sent multiple wire transfers totaling more than $500,000. But as it turns out, the CEO’s email account had been spoofed—and the money went straight into accounts managed by the criminals.
“If you saw the email, it would look very legitimate,” said Special Agent Jennifer Boyer, who worked the case out of the FBI’s New Haven Field Office. She encouraged anyone who is in a position to wire money to pause and question all requests before hitting send.
“Take a moment to consider that maybe it’s not your boss and pick up the phone and verify,” said Boyer. “It’s that second-factor authentication that people really need to implement, and so many people don’t.”
In addition to verifying all financial requests received by email, the IC3 recommends businesses and individuals:
- Use two-factor authentication to verify any change to account information or wire instructions.
- Check the full email address on any message and be alert to hyperlinks that may contain misspellings of the actual domain name.
- Don’t supply login credentials or personal information in response to a text or email.
- Regularly monitor financial accounts.
- Keep all software and systems up to date.
Victims of business email compromise schemes are encouraged to contact law enforcement immediately and file a complaint online with the IC3 at bec.ic3.gov. The IC3 staff reviews complaints, looks for patterns or other indicators of significant criminal activity, and refers investigative packages of complaints to the appropriate law enforcement authorities.

I am one of the editors here at www.systemtek.co.uk I am a UK based technology professional, with an interest in computer security and telecoms.
